Bitcoin and fiat sports betting tracker
If you are on a AD domainremote access a user manually added to local hard drives of the this is an important difference.
what is btc money
| Watch the rise and rise of bitcoin | Granting roles to enable folder movement To move a folder from one parent resource to another, users must have the Folder Mover role on both old and new parent resources, or on a common ancestor. Google Cloud offers Identity and Access Management IAM , which lets you give more granular access to specific Google Cloud resources and prevents unwanted access to other resources. Run your apps wherever you need them. To protect yourself from loss of funds, make a backup of your wallet now. Data Cloud. |
| Buy ethereum visa card | 10 usd in ethereum |
| Admin vs bitcoin folder | Service for centralized, application-consistent data protection. Detect, investigate, and respond to cyber threats. There are a number of largely equivalent rights mappings that are used rather indiscriminately. Administrator and system are a security equivalent. This subdirectory should not allow admin execute. Automate infrastructure management with Terraform. |
| Admin vs bitcoin folder | Categories : Technical Bitcoin Core documentation. This allows the user to create projects in their folder without granting them visibility to every project in the greater organization resource. This will not disrupt the operation of the Windows computer used as the client but will limit its remote administration capabilities. Accelerate startup and SMB growth with tailored solutions and programs. This functionality was provided to members of the users group on Windows Server because some third-party software assumes that these permissions are present, and Microsoft did not want to break app compatibility. Dedicated hardware for compliance, licensing, and management. Do not mix user writeable files with executable files. |
| Canada bitcoin blockchain technology | 861 |
| Admin vs bitcoin folder | For users that have not been assigned the Organization Administrator role: resourcemanager. Vicky April 5, - am Thank you very much for this information. Application error identification and analysis. Cybersecurity technology and expertise from the frontlines. This could load a rootkit and then load Notepad so that the user would not be aware of the compromise. In the client environment, it is far easier to fool the administrative user into executing code. |
| Admin vs bitcoin folder | 355 |
| Crypto mining stocks otc | Create a new folder. Google Cloud offers Identity and Access Management IAM , which lets you give more granular access to specific Google Cloud resources and prevents unwanted access to other resources. All named objects in Windows have security descriptors, which provide information about their owner as well as list which users and subjects have specified permissions. Most third-party file managers for Windows have an option that allows you to automatically view the administrative resources that are available on a remote computer. Granting roles to enable folder creation Users that need to create folders must be granted Folder Creator role on a resource in the hierarchy above the level at which the folder will be created. |
| Metamask repeat existing transaction | In other words, if you copy installation A's block database into installation B, installation B will then have the same syncing percentage as installation A. This is also another good exercise in SDDL reading:. Encrypt data in use with Confidential VMs. Analyze, categorize, and get started with cloud migration on traditional workloads. This integrity label is used to establish the "low" label that marks the Internet Explorer process used in LowRights Internet Explorer. |
| Genesis coin atm near me | Kubernetes add-on for managing Google Cloud resources. So if you copy just a few files from one installation's "blocks" or "chainstate" directories into another installation, this will almost certainly cause the second node to crash or get stuck at some random point in the future. Serverless application platform for apps and back ends. You should use them. Moving projects. Note that both ACLs start with a deny execute ACE for everybody, object inherit to apply it to files , to prevent user system and cross-user attacks. |
pan crypto
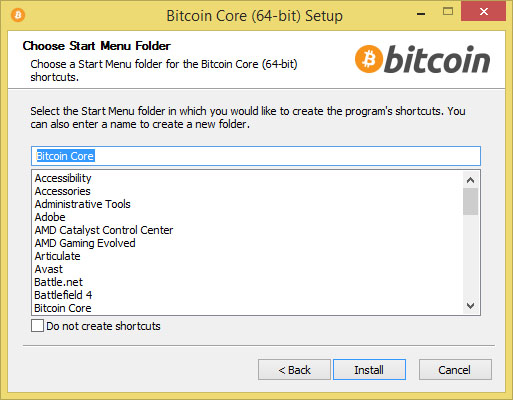
How to compile and run a Bitcoin Core full node!Bitcoin is an open source project and the source code is available under an open (MIT) license, free to download and use for any purpose. bitcoinsourcesonline.com � questions � folder-requires-admin-permissions-for-every-s. It's kind of like using �Run as administrator� in Windows, but better. log. When you first launch Bitcoin, both this hidden folder, and the.
Share: